
How AI Aids Post-Breach Analysis
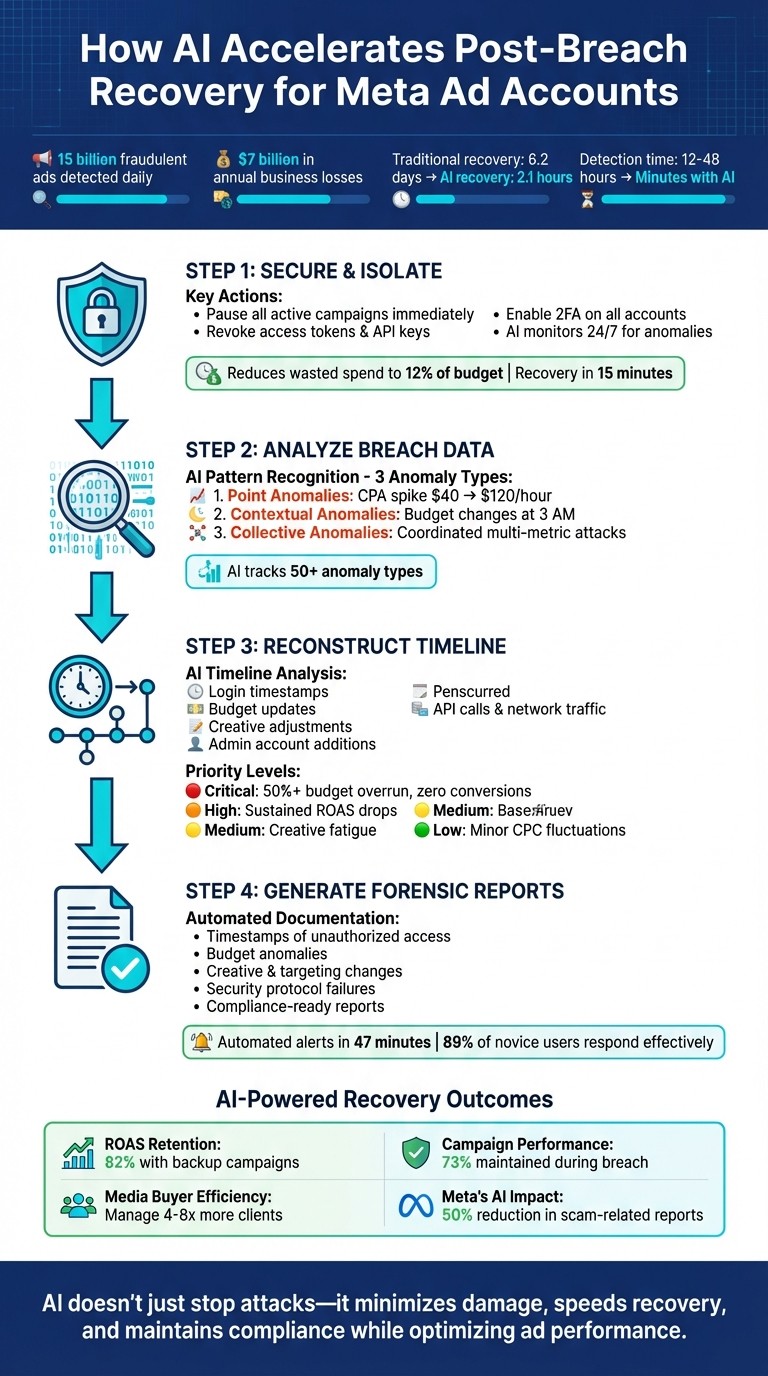
AI speeds detection, forensic analysis, timeline reconstruction, and automated recovery for breached Meta ad accounts to minimize damage and downtime.
Cyberattacks on Meta ad accounts are on the rise, with billions of fraudulent ads served daily, costing businesses $7 billion annually. AI tools are now critical for post-breach recovery, offering faster detection, automated responses, and detailed forensic insights.
Here’s how AI helps:
Real-time monitoring: AI flags suspicious activities like sudden budget spikes or logins from unusual locations, reducing detection delays from 12–48 hours to minutes.
Forensic analysis: Machine learning identifies patterns in log data, such as budget changes at odd hours or coordinated attacks across multiple metrics.
Breach timelines: AI reconstructs event sequences, pinpointing when and how breaches occurred.
Automated recovery: Tools like AdAmigo.ai pause compromised campaigns, replace affected ads, and restore performance within hours instead of days.
AI doesn’t just stop attacks - it minimizes damage, speeds up recovery, and helps businesses stay compliant with data breach reporting while optimizing ad performance.
4-Step AI-Powered Post-Breach Analysis and Recovery Process for Meta Ad Accounts
Step 1: Secure and Isolate the Breached Account
Revoke Access and Strengthen Security
The first step is to immediately pause all active campaigns. This stops attackers from draining your budget or running harmful content under your account. Head over to Business Manager to revoke access tokens, API keys, and any third-party integrations. Since attackers often use spyware capable of bypassing two-factor authentication (2FA), taking over accounts, intercepting SMS, or even stealing cryptocurrency, simply changing your password won’t cut it.
Make sure to enable two-factor authentication on Meta Ads and all other accounts and update every password, including those for your email and payment methods. Review account logs for any suspicious Meta ad activity, such as unfamiliar IP addresses or unexpected changes to admin roles. Using AI tools can help quickly detect these anomalies. Once your account is secure, keep AI monitoring active to flag irregular activities in real time.
Automate Anomaly Detection with AI
AI-driven platforms are incredibly effective for spotting unusual activity. They monitor your account 24/7, identifying behaviors like logins from unfamiliar locations, sudden spikes in spending, or unexpected campaign adjustments. Unlike manual monitoring, which can take hours or even days, AI tools can flag issues almost instantly.
These systems establish a baseline for normal account behavior. If something unusual happens - like a drastic budget increase or the addition of a new admin from an unknown location - the AI isolates the activity and sends an alert. This proactive approach not only helps minimize wasted ad spend (down to about 12% of your budget) but also drastically reduces recovery time to as little as 15 minutes.
Step 2: Analyze Breach Data with AI
Use AI for Pattern Recognition
Once you've isolated the breached account, it's time to dive into forensic analysis. This is where AI truly shines. It can sift through mountains of log data - everything from campaign changes and budget adjustments to login timestamps and IP addresses - at a speed no human could match. By flagging anomalies and analyzing deviations, AI helps uncover patterns that reveal the breach's full scope, similar to how it powers full-funnel AI optimization for performance.
AI typically identifies three types of anomalies:
Point anomalies: Sudden, isolated spikes, like your cost-per-acquisition skyrocketing from $40 to $120 within an hour.
Contextual anomalies: Irregularities tied to unusual timing, such as budget changes happening at 3 a.m. when your team is offline.
Collective anomalies: Coordinated shifts across multiple metrics, suggesting a broader, systemic breach.
Modern platforms can track over 50 types of anomalies, including audience hijacking, unauthorized budget reallocations, and suspicious pixel activity. A real-world example? Back in August 2025, a malvertising campaign used malicious ads to deploy malware capable of bypassing two-factor authentication and taking over accounts. AI tools excel at spotting the subtle data patterns and targeting shifts that signal these sophisticated attacks.
With these patterns identified, the next step is turning the raw data into actionable forensic reports.
Get Breach Insights with AdAmigo.ai
Once you've recognized the anomalies, tools like AdAmigo.ai's AI Chat Agent can help make sense of the data. This AI assistant translates raw Meta Ads logs into clear, actionable insights. You can ask it questions like, "What changed between February 20 and February 25?" or "Who made budget changes without authorization?" to quickly uncover breach specifics.
The AI can pinpoint which campaigns were altered, when unauthorized admins were added, and how much budget was misused. It also identifies root causes of performance issues, such as whether targeting changes, creative swaps, or pixel disruptions led to conversion drops during spending spikes. This level of detail doesn’t just tell you what went wrong - it helps you understand how the attackers operated and which vulnerabilities they exploited.
With this information in hand, you can prioritize recovery efforts based on the severity of the unauthorized changes, ensuring a faster path to compliance and regaining control.
Step 3: Reconstruct the Breach Timeline with AI
AI-Driven Timeline Builders
Reconstructing a breach timeline is all about pinpointing when unauthorized activities took place. After identifying anomalies, the next step involves sequencing these events to understand the attack's progression. AI-driven timeline builders make this process much easier by analyzing various logs - like access logs, campaign changes, API calls, and network traffic data. These tools piece together data from different sources, such as login timestamps, budget updates, creative adjustments, and admin account additions. The result? A clear, visual timeline that lays out when and how each unauthorized action occurred.
AI tools are particularly effective at identifying deviations by comparing timestamps against your account's regular activity patterns. For instance, if budget changes typically happen during business hours but the AI flags alterations made late at night, that’s a red flag. Tools like SIEM platforms (e.g., Splunk, Elastic) can also help correlate logs to detect entry points, such as when attackers bypass multi-factor authentication (MFA). This is especially important for Meta ad accounts, as Meta is the second most spoofed brand in credential phishing emails seen in 2024.
With this timeline in hand, the next step is to focus on the flagged changes and prioritize your recovery efforts.
Prioritize Anomalous Changes with AdAmigo.ai
Not all flagged changes are equally critical, and that’s where AdAmigo.ai’s AI Actions feature steps in. This tool categorizes anomalies into four levels of priority: Critical, High, Medium, and Low. For example, Critical alerts might include runaway spending that exceeds 50% of the budget or zero conversions caused by broken tracking. High-priority flags could highlight sustained ROAS drops or significant budget underpacing. Meanwhile, Medium and Low alerts might point to issues like creative fatigue or minor CPC fluctuations.
AdAmigo.ai’s alerts dashboard displays these anomalies in chronological order, making it easier to review the sequence of unauthorized actions. You can also track patterns across creatives, budgets, and targeting. The dashboard’s change-tracking and baseline-learning features allow you to compare current breach data with historical trends, helping you pinpoint which attack vectors caused the most harm. Instead of combing through endless logs, you’ll have a ranked list of actionable alerts. This means you can quickly reverse unauthorized budget changes, pause compromised campaigns, or restore original targeting settings - all without wasting time on unnecessary details.
Black Hat USA 2025 | Autonomous Timeline Analysis and Threat Hunting: An AI Agent for Timesketch
Step 4: Generate Automated Forensic Reports
Once you’ve pieced together a clear timeline, the next priority is documenting and visualizing every detail of the breach.
AI-Generated Insights for Compliance and Recovery
After reconstructing the timeline, it’s time to document all the breach details - something essential for both internal recovery efforts and meeting external compliance requirements. Traditionally, compiling forensic reports can take days, especially when pulling data from multiple sources like access logs, campaign changes, and billing records. AI tools simplify this process by quickly summarizing breach information into ready-to-use reports. These reports include critical details such as timestamps of unauthorized access, budget anomalies, creative adjustments, and targeting changes. They also identify where security protocols failed, such as instances where multi-factor authentication was bypassed or signs your Meta ad account is compromised.
For agencies juggling several client accounts, this automated reporting is indispensable. It ensures transparency and helps meet compliance deadlines by consolidating logs into a clear, actionable summary. These reports not only document what happened but also recommend safeguards to prevent future breaches, offering both clarity and direction.
Use AdAmigo.ai's Dashboards for Post-Breach Clarity
AdAmigo.ai takes this a step further by combining report generation with robust visualization tools. Its centralized audit trail organizes past anomalies in chronological order, making it easy to identify patterns across creatives, budgets, and targeting. You can also compare current breach data with historical trends to uncover recurring vulnerabilities or previously unnoticed issues before they escalate.
"AdAmigo Protect continuously monitors your ad accounts for anomalies, risks, and costly mistakes, and alerts you the moment something deviates from normal behavior." – AdAmigo.ai
The platform’s Smart Alerts provide real-time notifications for suspicious activity, such as sudden spikes in ad spend or hacking attempts, and instantly update your breach timeline. This comprehensive record - from the initial detection to recovery - makes client-facing reporting straightforward. It also highlights how the breach was managed and the measures taken to prevent future incidents. Recognized as a "High Performer" on G2, AdAmigo.ai is trusted for its thorough monitoring and reporting capabilities.
Use AdAmigo.ai for Post-Breach Recovery
When a breach disrupts your campaigns, having forensic evidence and a detailed timeline is just the start. The real challenge lies in restoring performance quickly while ensuring the breach isn’t exploited again or recovering disabled Meta ad accounts if the platform has already taken action. Manual recovery - redesigning ads, rebuilding audiences, and reworking budgets - can take days. AdAmigo.ai steps in to automate and accelerate this process, securing campaigns and optimizing Meta ad account structures in real-time.
Auto-Generate Secure Creatives and Campaigns
Compromised ads need to be replaced immediately. AdAmigo.ai's AI Ads Agent analyzes your top-performing historical ads and automatically generates fully designed, ready-to-launch ad creatives. With a single click, these can be deployed to your Meta ad account, cutting out time-consuming manual processes. This approach not only ensures rapid creative replacement but also allows you to test new audiences while keeping your brand identity intact.
AdAmigo.ai’s Backup Campaign Deployment system retains about 82% of the original ROAS by switching to pre-vetted, secure campaign structures. This minimizes performance dips during the transition and sets the groundwork for continuous improvement. By automating creative replacement, the platform helps you recover faster and more efficiently.
Continuous Optimization During Recovery
Recovery isn’t just about replacing ads - it’s about rebuilding momentum. AdAmigo.ai’s AI Actions feature provides a daily, prioritized to-do list of impactful changes, covering creatives, audiences, budgets, and bids. Performance is audited every 15 minutes, with real-time adjustments made based on your preset rules. You can opt for ["Autopilot Mode" for full automation or "Review Mode"] (https://www.adamigo.ai/blog/meta-ads-ai-manual-vs-autopilot-recommendations) to manually approve suggestions, ensuring you stay in control during critical periods.
The AI Quarantine System plays a key role, maintaining 73% of campaign performance during breaches and cutting wasted spend to just 12% of the budget, compared to the typical 15–20% overruns seen with manual recovery. This continuous optimization not only restores campaign performance but also strengthens your account against future threats.
"Our budgets are controlled, our spend is being smartly allocated and our ROAS is up massively. Agencies charging 7 times the cost of AdAmigo have been put to shame." – Rochelle D. from G2 Review
AdAmigo.ai’s learning agent constantly improves its recovery strategies by testing and scaling high-performing variations faster than any human team could. This connected system - optimizing creatives, targeting, bids, and budgets - helps campaigns stabilize in just 2.1 hours, compared to the 6.2 days typically needed for manual recovery.
Conclusion
Meta ad account breaches are becoming more advanced and frequent. Between 2024 and 2025, up to 15 billion high-risk fraudulent ads were detected daily, generating around $7 billion annually. Meanwhile, manual forensic analysis not only drains budgets but also slows down campaigns, leaving businesses vulnerable.
AI tools are stepping in to revolutionize post-breach recovery. By automating tasks like anomaly detection, pattern recognition, timeline reconstruction, and forensic reporting, these tools significantly reduce response times. For example, AdAmigo.ai can issue automated alerts within just 47 minutes, allowing 89% of novice users to respond quickly and effectively.
These tools don’t just stop at containment. They also help businesses optimize their resources. With AI handling performance reviews, security monitoring, and campaign rebuilds, a single media buyer can manage four to eight times more clients than before.
As generative AI continues to increase the risks of ad scams, proactive AI solutions are becoming essential. Over an 18-month period ending in late 2025, Meta removed or rejected more than 46 million ads from Chinese resellers, cutting scam-related ad reports by over 50%. For small and medium-sized businesses, adopting AI for real-time monitoring, automated breach isolation, and detailed forensic insights ensures faster recovery and helps maintain a competitive edge.
FAQs
What should I do first after a Meta ad account breach?
If your Meta ad account has been breached, act quickly to secure it. Start by enabling two-factor authentication to add an extra layer of security. Next, review and update user access to ensure only trusted individuals have permissions. Check recent activity to identify any suspicious actions or changes. Finally, take advantage of Meta's security tools to strengthen your account's defenses. These steps can help protect your account and stop further unauthorized activity.
What data should I export for AI-driven breach forensics?
Exporting key data is crucial for effective analysis and reporting. Make sure to include campaign details, targeting settings, creative assets, budget and bid configurations, performance metrics, and security logs. By compiling this information, AI tools can better evaluate the situation and provide actionable insights on the breach.
How can AI help prove what happened for compliance?
AI plays a crucial role in uncovering the details of a breach by offering real-time detection, in-depth analysis, and automated reporting. Tools such as AdAmigo.ai can pinpoint unusual activities, create timelines, and map out the extent of the breach. Additionally, AI generates forensic reports that outline the cause, the steps taken to respond, and measures for mitigation - helping organizations stay compliant with regulations like GDPR and CCPA. By automating log collection, AI also simplifies demonstrating adherence to security standards and regulatory requirements.